CYBERSECURITY
Yacht SecuritySuperyacht Cybersecurity Solutions
Aligned with internationally recognised best practice frameworks, our superyacht cybersecurity solutions provide a complete and comprehensive cyber risk management service. Our team of skilled engineers can implement bespoke and tailored cyber solutions, protecting yachts from external threats and enabling vessels to maintain full IMO compliance.
“We provide an effective but pragmatic approach to cyber risk management and believe that security solutions need not be invasive, but a beneficial addition to existing operations.”
Managed Cybersecurity Solution
We offer a comprehensive solution for superyachts, providing everything vessels need to run secure and cybersafe operations at sea.
Key Service Areas
Our solution addresses the following key areas, offering an holistic solution with advanced features and benefits aligned with yacht business operations.
Governance
We undertake a cybersecurity audit and risk assessment to develop a cyber management plan with supporting policies and procedures incl. an incident response plan.
Network Security
This includes ensuring your network meets secure network configuration standards (determined through expert consultancy), along with issuing bespoke documentation.
Crew Awareness Training
We provide a modular cyber awareness training course that supports the new policy requirements to deliver cybersecurity compliance. Find more details here.
Asset Management
All assets are identified and registered in our secure online system documentation platform and network monitoring ensures that critical device outages are detected in real time along with any new devices joining the network.
Password Management
We provide crew with a password management solution which includes a built in MFA authenticator. Particularly useful for rotational crews.
Computer Management
Vessels benefit from a comprehensive list of tools, curated by our cyber experts. This includes patch management, endpoint protection, software audits and much more.
Mobile Device Management
The above benefits are extended to mobile devices, with patch management and the ability to remote wipe devices in case of loss/theft.
Email Service
We provide everything you need to ensure your onboard email service is secure. This includes enhanced spam protection and audit logs. We also provide Microsoft office applications.
Advanced File Management
Share files securely with crew, suppliers, guests and owners. We provide a secure file sharing system (with a mobile app) with features such as managed access control. Data is also encrypted and we provide an off vessel data backup service.
Incident Response Management
We will provide documentation and policies for crew to follow in the event of an incident. Our ongoing cybersecurity service as detailed above will detect faults or anomalies, which our team will work to overcome.
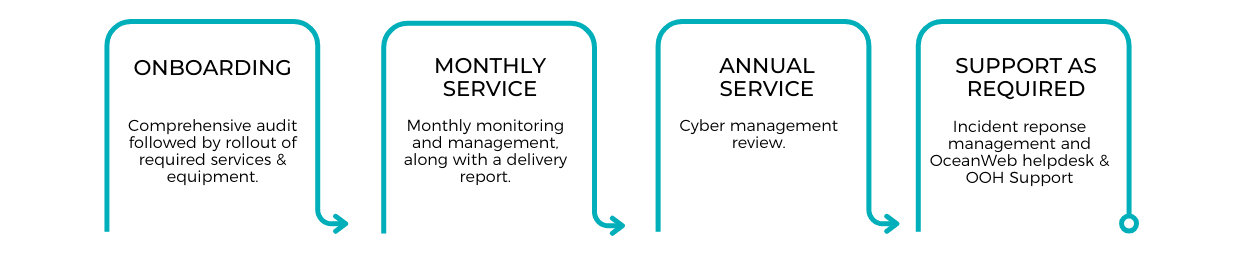
Service Delivery

Crew Cyber Awareness Training
Yacht crew pose the most significant threat to maritime cyber security on board, impacted by knowledge gaps and the rotational nature of superyacht crew.
CyberSafe is our modular cyber awareness training course that supports the new IMO policy requirements to deliver maritime cyber security compliance.
Quick and interactive
90+ Modules
Reporting feature
Audit and Vulnerability Assessment
In addition to our comprehensive cybersecurity solutions, we offer detailed assessments as a one-off service.
Cyber Audit
This is a detailed examination of your IT infrastructure, policies, and procedures to ensure they meet industry standards and best practices. During the audit, we assess your systems for compliance with relevant regulations, identify any gaps in your security posture, and provide actionable recommendations for improvement.
Vulnerability Assessment
Our assessment systematically probes your network, systems, and applications to detect known vulnerabilities, such as unpatched software, misconfigurations, or exposed services that could be exploited by cybercriminals.


Secure your vessel with OceanWeb
Contact our team to discuss your vessels cybersecurity requirements. We offer bespoke plans based on yacht’s requirements and size.